When the pandemic forced millions of employees to suddenly work from home, it came at a huge cost to company security — leaving IT security teams unprepared to scale their data security responsibilities. To protect their companies, some turned to stricter protocols to better monitor internal threats, including verifying employee identities with facial recognition software. But with the rising backlash against facial recognition biometric technology, many are now searching for a less privacy-invasive way to authenticate their remote workforces.
This article explores how facial recognition technology is used to prevent insider threats, and shares why employers must find identity authentication solutions that are secure, but focus on privacy and employee convenience.
What are insider threats? And is company data secure in remote workforce environments?
Insider threats in cyber security are threats posed by individuals from within an organization, such as current or former employees, contractors and partners. These individuals have the potential to misuse access to networks and assets to intentionally or unintentionally modify, delete, or disclose sensitive information. Data security includes all the steps that a company takes to protect this sensitive data.
This is especially critical for remote workforces, where insider threats and negligent employee behavior present a real risk for companies when employees handle sensitive or privileged information in insecure work-from-anywhere environments. In just the last two years, there was a 44% increase in insider threats incidents. It’s important to remember that insider threats include both malicious insiders who purposely steal data, money, or other assets, and negligent insiders — usually employees making a human error such as falling prey to a phishing attack or sharing their devices with an unauthorized user.
To truly protect endpoint devices such as work laptops when you can no longer physically see employees in the traditional physical office, security teams must have additional security protocols such as continuous authentication to limit the risk of insider threats.
What is continuous authentication, and why do companies need it?
There are many use cases for continuous authentication, but all in all, continuous authentication ensures that only authorized users gain access to sensitive information by requiring employees to continuously prove their identities while they’re accessing company devices.
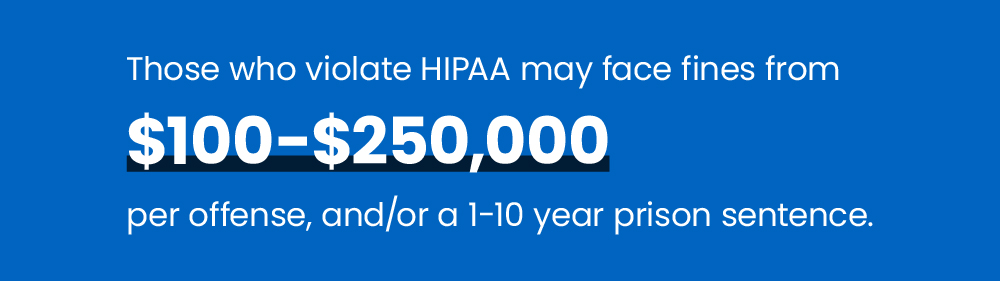
Let’s use an example. I’m Employee 1 working from home and my job is medical data entry of patient files. My teenager’s laptop battery has died, so I innocently gave him my company laptop so he can finish watching Netflix for a few hours. Simply by sharing my work computer that contained sensitive medical information with an unauthorized user, I’ve committed a HIPAA violation — potentially causing my employer hundreds of thousands of dollars. But if this work laptop had continuous authentication, it would ensure that only Employee 1 had access to the company device at all times, blocking unauthorized users from ever getting access to the sensitive patient or company data.
Companies from highly regulated industries such as medical, finance, legal, and human resources have to follow strict standards to safeguard customer and company data. So how can employees prove their identities throughout the day without it being a burden? Many security teams turned to facial recognition, using the laptops camera to authenticate their employees faces. But even though facial biometric was secure, the benefits were quickly outweighed with employee privacy concerns.
How is facial recognition software typically used?
Inherently intrusive, facial recognition looks at various facial characteristics to create a personal and identifiable user profile, which public and private enterprises can use for identification and identity validation purposes.
In the business world, facial recognition is used in physical offices to record employees’ attendance and monitor their activity, while companies working remotely use facial recognition to track productivity and work presence from home.
Why facial recognition software is losing popularity as a security practice

The skeptical public
Facial recognition technology has been under the microscope as organizations and lawmakers re-evaluate its use in the wake of global protests about racial injustice. Technology giants Amazon, IBM and Microsoft all recently announced that they would stop selling facial recognition technology to police departments in the United States, citing the technology’s potential for violating human rights and concerns about racial profiling.
As a result, the skeptical public view on facial recognition makes the technology less attractive for its deployment in business practices. A powerful recent example is Meta’s announcement of shutting down its facial recognition system on Facebook, which automatically recognized people in photos and videos, moving the company towards a more limited use of their facial recognition technology.
And in the workplace, authenticating employees by scanning their faces using their laptop’s camera introduces even more privacy concerns (and feels inherently intrusive), particularly when employees are working from home — causing massive pushback against employers.
Accuracy and bias concerns with using facial recognition in the workplace
Facial recognition technology has been under the microscope as organizations and lawmakers re-evaluate its use in the wake of global protests about racial injustice. A study showing gender and skin-type bias of facial recognition technology, prone to misclassifying darker-skin-tone women. The IRS also caught headlines recently with Americans taking a stand on how they want their personal data to be handled.
High false negative and false positive rates in facial recognition accuracy add to the cost of maintaining such security measures. IT departments have to solve situations where the right employees are locked out, or unauthorized employees are granted access to confidential data. Overall, this leads to damaged employee productivity, high costs, and diminished efficacy when facial recognition is used as an Identity and Access Management system.
So how can employees prove their identities throughout the day without invading employee privacy?
Employers must find the right balance of security, privacy and convenience. Let’s explore some popular options:
- Facial recognition is a no-go. Using the laptop’s camera results in privacy concerns and feels intrusive — particularly when employees are working from home.
- Asking workers to use an authenticator app multiple times a day adds quite a bit of friction. Employees are also generally hesitant about downloading company-sponsored apps on their personal phones.
- External hardware like fingerprint scanners are expensive and employees have concerns about how that fingerprint data will be handled.
The future of remote employees authentication is user-friendly and privacy-focused

Any business which handles customer data on employees’ devices should be able to tell at any time throughout the day whether unauthorized users are accessing the company endpoints — with processes in place to flag suspicious behavior and take action.
But with a shift in paradigm and more importance placed on privacy, employees are less open to sharing their personal (especially biometric) data without a good reason for it — requiring employers to come up with less intrusive, more user-friendly methods to verify their identities.
Protecting customer data is easy with continuous authentication solutions like TypingDNA’s ActiveLock, helping you make the most of modern behavioral biometrics authentication technologies without infringing on employees’ privacy rights or affecting their productivity.
ActiveLock is built to be user-friendly and puts privacy first. It analyzes how an employee types on their work laptop, NEVER what they type. So regardless if that employee decided to intentionally share their device or someone tries to use an employee’s computer without their knowledge — the result is the same. If ActiveLock can’t authenticate the user, it will take instant action to lock the company device or send a silent alert notifying the security team.