
Category: MFA


Workforce MFA/2FA method that doesn’t require personal phones
Updated June 2025 To achieve security, enterprises work with IAM systems that deploy multi-factor authentication (MFA), or simply two-factor authentication (2FA). MFA allows businesses to verify their employees’ identities when they log in to corporate apps. While MFA is key to security, companies should avoid using methods that require employees to use their phones. Below,…
Netflix Password Sharing Crackdown: Why It’s Good For Business
The Netflix password sharing crackdown has begun. And while the announcement left some streaming fans nervous about how the limit on password and account sharing will impact their entertainment experience, reducing account sharing can potentially bring a nice chunk of change for Netflix — upwards of $1.6 Billion per year by charging password-sharing users extra…
User-friendly, typing biometrics-based alternative to TOTP authentication
TOTP was first introduced by RSA Security and was exclusively sold under patent. Once the patent expired, TOTP gained momentum and was adopted on a large scale as 2FA became more popular.
What Is Multi Factor Authentication (MFA) and Why Passwords Are Not Enough
With cyber breaches making headlines seemingly every week, one thing is clear — passwords alone are no longer enough to keep us safe. While stopping all online crime is not a realistic goal, Multi Factor Authentication (MFA) is a simple but critical step in your security flow that can massively reduce the likelihood you or your…
How to improve your OTP authentication using typing biometrics
This article will highlight three implementation forms of OTP authentication and present a valid alternative or coupling method that provides increased security without harming the user experience.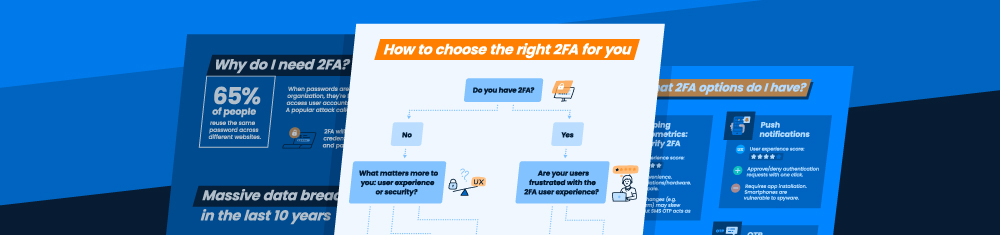
Cheat Sheet: How to Choose the Right 2FA for Your Website
With the next cyber breach around the corner, having 2FA on your website is a no brainer. But which two-factor solution is right for you? There’s plenty to consider in making the right decision. Do you need high security or more convenience? Do you want a balance of both? With this 2FA guide, we’ll help…
How to secure remote access for employees working from home
How do you maintain secure remote access when employees work remotely? That was the million dollar question even before the COVID-19 pandemic forced millions of employees to transition to working from home — practically overnight. With more and more employees and contractors working remotely, the cybersecurity threats that organizations face have drastically changed. So how…
Benefits of an AI-powered MFA Setup
The need for a robust and secure MFA solution is obvious with the rise in frequency (and sophistication) of cyberattacks. IS engineers and product managers frequently struggle to choose between the ease of integration, security, and end-user experience when optimizing their MFA. In this article, we’ll share an AI-powered MFA setup that answers not only the integration concerns that IT departments might have, but also addresses questions about user adoption and great UX.