
Blog


PCI DSS Compliance Requirements for Remote Work: 5 Things You Must Know
If your business handles credit card and payment information, you’re responsible for keeping that cardholder data secured by obeying the Payment and Card Information Security Standard (PCI DSS) compliance requirements. But when your workforce is remote and your endpoints are unprotected, keeping that data safe is an unprecedented challenge facing today’s security teams. As more…
Windows Defender for Endpoint Can Stop a Cyberattack, But Not Device Sharing
Windows Defender for Endpoint and similar antimalware/antivirus systems are all pretty good at analyzing incoming cyber threats that target endpoints, and responding to virus threats. But, what these systems fail at is providing visibility into whether the employee you trusted with that company endpoint is the one who’s actually accessing it throughout the entire workday —…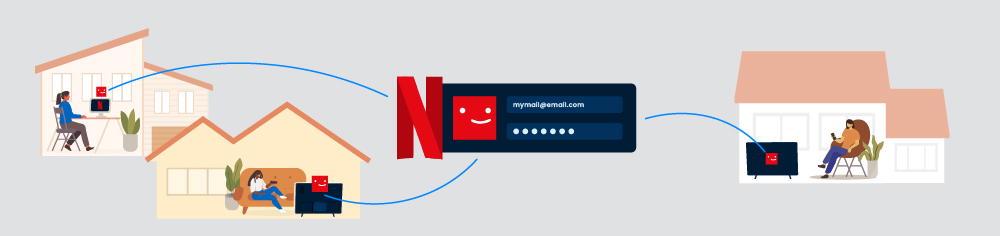
Netflix Password Sharing Crackdown: Why It’s Good For Business
The Netflix password sharing crackdown has begun. And while the announcement left some streaming fans nervous about how the limit on password and account sharing will impact their entertainment experience, reducing account sharing can potentially bring a nice chunk of change for Netflix — upwards of $1.6 Billion per year by charging password-sharing users extra…
Working from home call center equipment to ensure customer data security
From laptops to headphones, call center employees working remotely require the right equipment to be successful. But working from home presents an even bigger challenge: sensitive customer data is now spread across thousands of company laptops — so knowing who is accessing your company’s devices at all times becomes increasingly important. Below, we explore why…
Expert Insights Awards TypingDNA Best of Zero Trust Solutions, Plus 2 More Cybersecurity Categories
On April 12th, 2022, Expert Insights announced their “Best Of” Cybersecurity awards — declaring TypingDNA as the winner across 3 major categories. Expert Insights declared TypingDNA as the winner across 3 cybersecurity categories: Best of Zero Trust Security (ActiveLock) Best of Multi-Factor Authentication (Verify 2FA) Best of Biometric Authentication (ActiveLock and Verify 2FA) Expert Insights…
HIPAA compliance checklist for remote employees in 2022
With rising cyber threats and more people working from home, securing endpoint devices has never been more critical. In the healthcare industry, the Health Insurance Portability and Accountability Act (HIPAA) protects private and sensitive patient data by requiring organizations handling healthcare information to pay closer attention to their protocols and institute airtight security safeguards. Hospitals,…
Cybersecurity Executive Order 14028: What You Need to Know for 2022
In May of 2021, the Biden administration took a big step toward modernizing the cyber defense of the United States. As a response to the growing number of high profile security breaches, President Biden signed Cybersecurity Executive Order 14028 “Improving the Nation’s Cybersecurity” — with the goal of protecting federal networks from cyber threats. It…
If Using Facial Recognition Software for Workforce Authentication, STOP
When the pandemic forced millions of employees to suddenly work from home, it came at a huge cost to company security — leaving IT security teams unprepared to scale their data security responsibilities. To protect their companies, some turned to stricter protocols to better monitor internal threats, including verifying employee identities with facial recognition software….